Critical Infrastructure
Ground truth for critical sectors
Your surface is larger
than you think
Critical infrastructure operators struggle to track internet-facing assets because of acquisitions, aging systems, and decades of technical debt. Standard surface management tools may miss an old domain name from a legacy subsidiary, a test server that never got commissioned, or a forgotten WiFi access point in a regional facility parking lot.
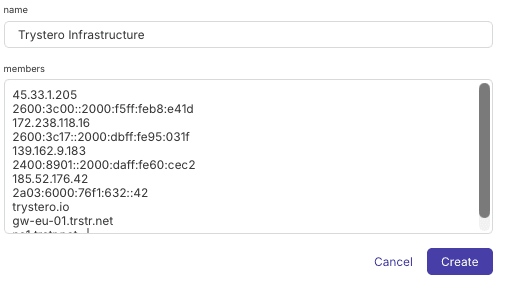
Oscar maps your complete internet surface by following the connections that define internet infrastructure. Starting from known assets, we discover forgotten domains, acquisition remnants, and backend infrastructure never intended for public access. Our Mosaic reveals how logical and physical infrastructure connect—from domain names to IP addresses to the actual routers and facilities where your data lives.
Enter domains, ASNs, or IP ranges. Oscar expands from these seeds, discovering related infrastructure through certificates, shared hosting, routing relationships, and configuration patterns.
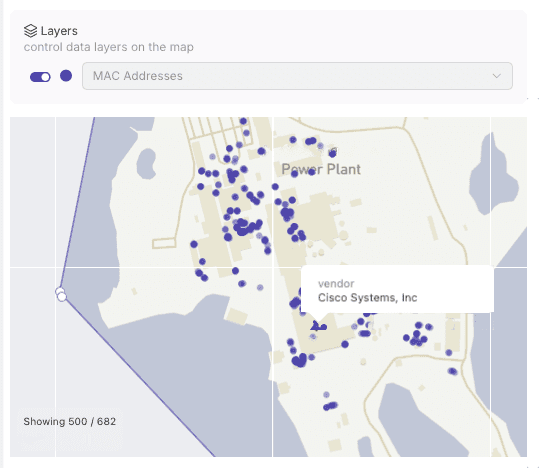
Visualize domains, IPs, certificates, and services across your entire infrastructure. Geofencing identifies wireless and IoT devices near critical facilities.
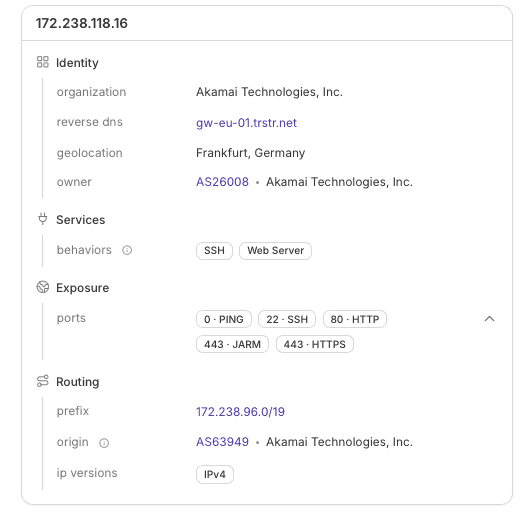
See open ports, running services, and software versions across all discovered assets. Identify forgotten assets, shadow IT, and acquisition remnants that create exposure.
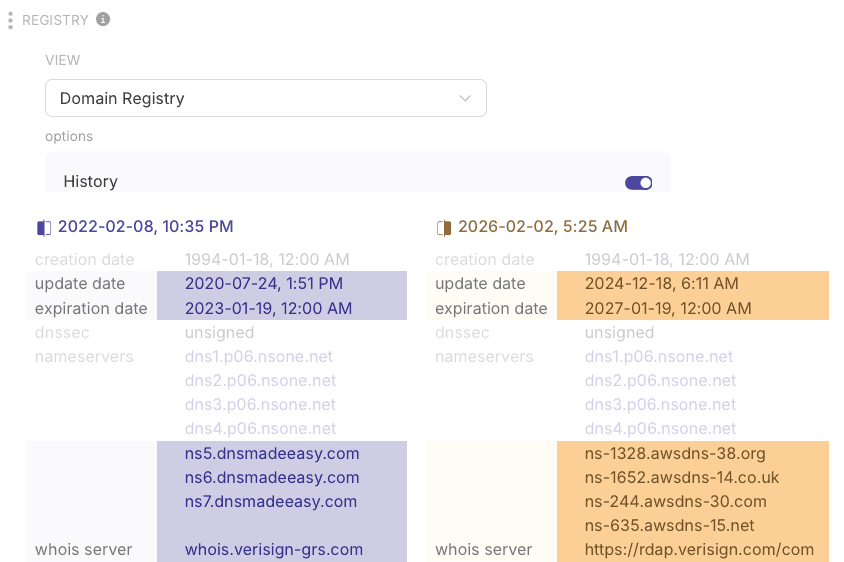
Monitor new assets as they appear. Identify configuration changes that create exposure. Historical views show evolution and can identify patterns of interest.
Our global collector network ensures we find assets hosted anywhere, not just in known and expected locations. Certificate transparency logs expose internal hostnames and services. Port scanning identifies what’s actually running: mail servers, VPN gateways, forgotten web applications. Reverse DNS offers clues to infrastructure purpose.
Geofencing near your facilities discovers wireless devices and IoT infrastructure invisible to traditional scanning. Historical data shows how your infrastructure has evolved, tracking decommissioned services that might still be partially exposed and infrastructure changes in response to vulnerabilities.
This data adds up to a complete picture of your internet exposure—the assets you knew about, and the parts you’d forgotten.